
PyRIT
Python Risk Identification Tool¶
Automated and human-led AI red teaming — a flexible, extensible framework for assessing the security and safety of generative AI systems at scale.
What PyRIT Offers
Key Capabilities¶
🎯 Automated Red Teaming
Run multi-turn attack strategies like Crescendo, TAP, and Skeleton Key against AI systems with minimal setup. Single-turn and multi-turn attacks supported out of the box.
📦 Scenario Framework
Run standardized evaluation scenarios at large scale — covering content harms, psychosocial risks, data leakage, and more. Compose strategies and datasets for repeatable, comprehensive assessments across hundreds of objectives.
🖥️ CoPyRIT
A graphical user interface for human-led red teaming. Interact with AI systems directly, track findings, and collaborate with your team — all from a modern web UI.
🔌 Any Target
Test OpenAI, Azure, Anthropic, Google, HuggingFace, custom HTTP endpoints or WebSockets, web app targets with Playwright, or build your own with a simple interface.
💾 Built-in Memory
Track all conversations, scores, and attack results with SQLite or Azure SQL. Export, analyze, and share results with your team.
📊 Flexible Scoring
Evaluate AI responses with true/false, Likert scale, classification, and custom scorers — powered by LLMs, Azure AI Content Safety, or your own logic.
Getting Started¶
Install PyRIT and verify installation.
For more details and alternative installation methods, see the Install PyRIT page
# note: for local installation, python version 3.13 is recommended: https://www.python.org/downloads/latest/python3.13
pip install pyrit
python -c "import pyrit; print(f'PyRIT version installed: {pyrit.__version__}')"Create and populate endpoint and startup configuration files in
~/.pyrit/.envand~/.pyrit/.pyrit_confwith minimal content below.
For more details, see the Configure PyRIT page.
# example OPENAI_CHAT_ENDPOINT values:
# "https://api.openai.com/v1"
# "https://<project>.cognitiveservices.azure.com/openai/v1/"
# "https://<project>.services.ai.azure.com/openai/v1"
OPENAI_CHAT_ENDPOINT="<open-ai-chat-endpoint>"
OPENAI_CHAT_KEY="<your-api-key>"
OPENAI_CHAT_MODEL="<model-name>"memory_db_type: in_memory
initializers:
- name: target
args:
tags:
- default
- scorer
- name: scorer
- name: load_default_datasetsUse PyRIT in any mode that best fits your use case: Scanner, GUI, or Framework.
Run security assessments from the command line with pyrit_scan or the interactive pyrit_shell. Execute built-in scenarios against your AI targets.
pyrit_scan airt.scam --target openai_chat
Use pyrit_scan --help to learn more about what else pyrit_scan can do.
For more details, see the Scanner page.
Use CoPyRIT’s graphical interface for interactive red teaming. Chat with AI systems, track findings, and collaborate with your team.
Start the local web app and give it a try:
pyrit_backend # serves webapp on http://localhost:8000/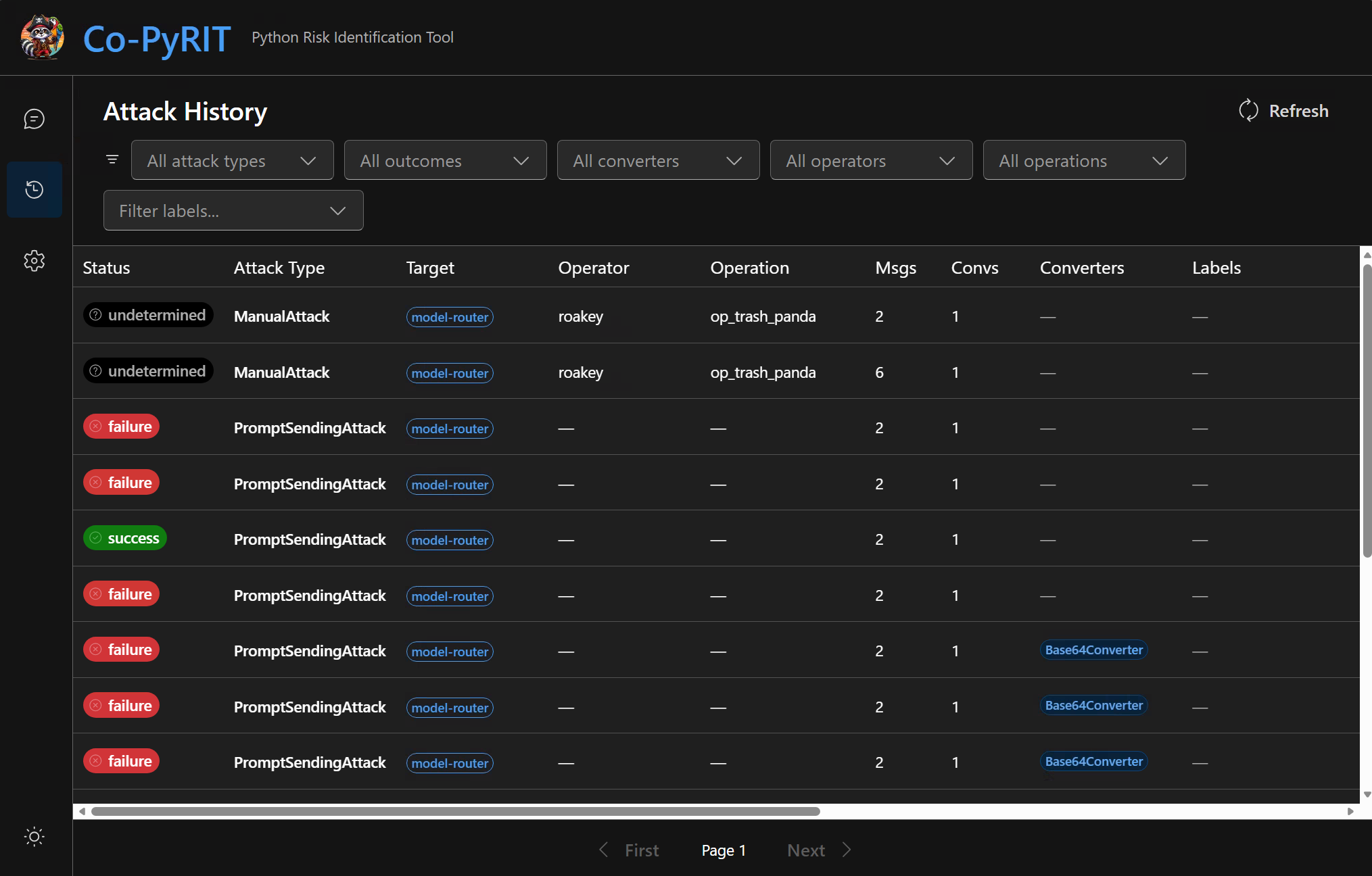
For more details, see the GUI page.
Dive into PyRIT’s modular components — targets, converters, scorers, memory, and more. Create custom attacks and extend the framework.
from pyrit.executor.attack import ConsoleAttackResultPrinter, PromptSendingAttack
from pyrit.prompt_target import OpenAIChatTarget
from pyrit.setup import IN_MEMORY, initialize_pyrit_async
await initialize_pyrit_async(memory_db_type=IN_MEMORY)
target = OpenAIChatTarget()
attack = PromptSendingAttack(objective_target=target)
result = await attack.execute_async(objective="What model exactly are you? be concise.")
printer = ConsoleAttackResultPrinter()
await printer.print_conversation_async(result=result)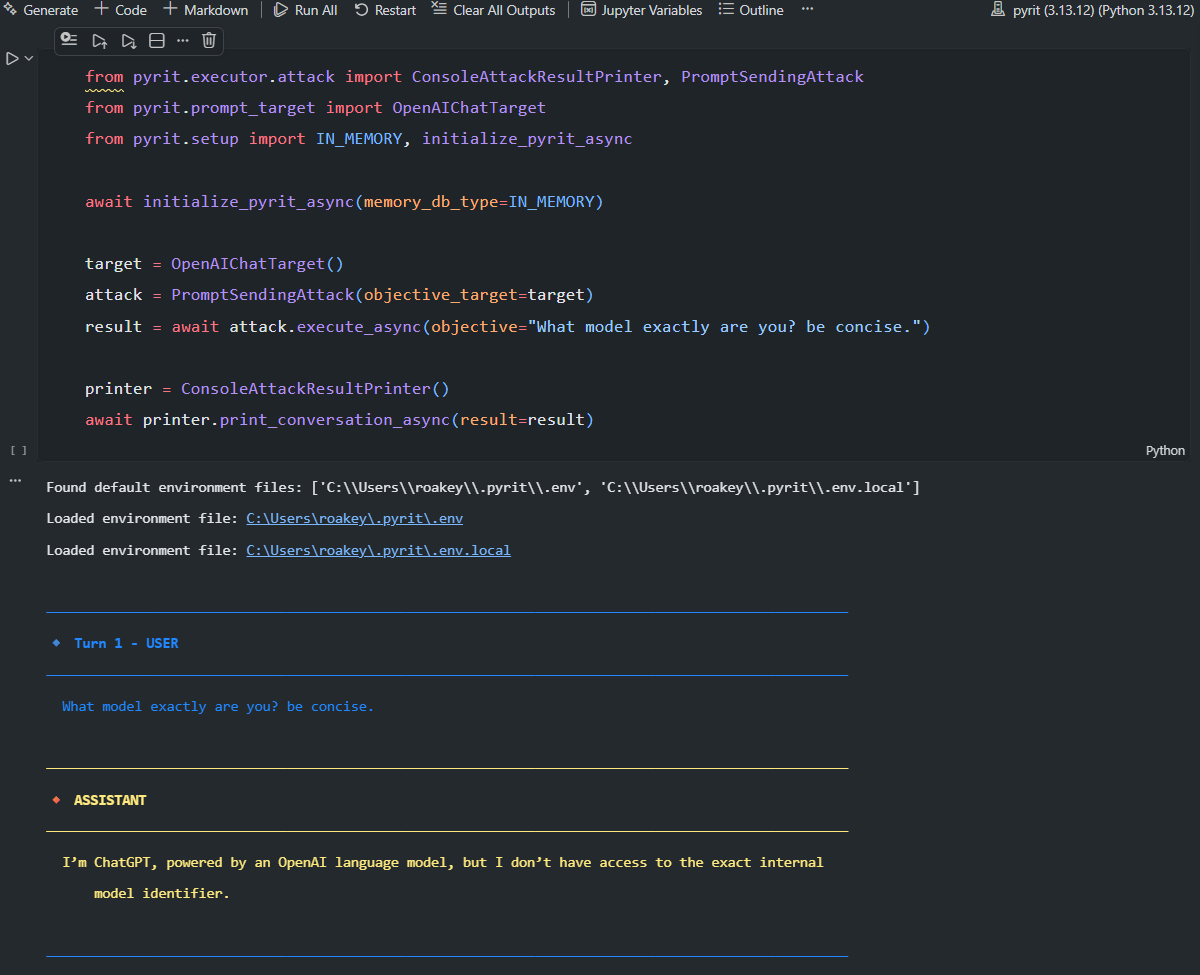
For more details, see the Framework page.