Unified SSO with Copilot Agent and D365 Omnichannel
This sample app demonstrates unified SSO with Copilot Agent and D365 Omnichannel using a 3rd party authentication provider.
Use Case: C2 get authenticated to Copilot agent and D365 Omnichannel at the start of the session. C2 can get authenticated / private information from Copilot agent and continue to have secure conversation with live agent on agent handover.
Detailed Instructions - Run on local machine
1. Setup Public Key / Private Key:
OPTIONAL - This sample app comes with per-configured public/private keys. This step is optional if self generated keys are not required.
-
Install Git Bash on your machine.
-
Generate a private key by running the command on git bash.
openssl genpkey -algorithm RSA -out private_key.pem -pkeyopt rsa_keygen_bits:2048
- Open the
private_key.pemusing text editor. Copy the key and update thePRIVATE_KEYenvironment variable in.envfile in the root folder.
Make sure the entire text is copied beginning with “—–BEGIN PUBLIC KEY—–” and ending with “—–END PUBLIC KEY—–”.
- Generate a public key file by running the command on git bash.
openssl rsa -pubout -in private_key.pem -out public_key.pem
- Rename the file
public.keyand save the file in/keysproject folder.
2. Host public key URL:
Execute the given commands as given in each step. Replace
<>with your appropriate values.</em>
-
Clone the repository
` git clone
` -
Navigate to your project directory.
cd <your-project-folder> -
If your identity is associated with more than one subscription, then set your active subscription to subscription of the storage account that will host your static website.
az account set --subscription <subscription-id>- Replace the
<subscription-id>placeholder value with the ID of your subscription.
- Replace the
-
Create Azure Storage Account.
` az storage account create –name
--resource-group --location --sku ` - Replace the
<mystorageaccount123>placeholder value with the name of your storage account. - Replace the
<myresourcegroup>placeholder value with the resource group where you want to create the storage account. - Replace the
<eastus>placeholder value with the location of storage account. - Replace the
<Standard_LRS>placeholder value with the storage account SKU.
- Replace the
-
Enable static website hosting.
` az storage blob service-properties update –account-name
--static-website --404-document --index-document ` - Replace the
<storage-account-name>placeholder value with the name of your storage account. - Replace the
<error-document-name>placeholder with the name of the error document that will appear to users when a browser requests a page on your site that does not exist. - Replace the
<index-document-name>placeholder with the name of the index document. This document is commonly “index.html”.
- Replace the
-
Upload public key to the $web container from a source directory..
` az storage blob upload-batch -s
-d '$web' --account-name --content-type 'text/html' ` - Replace the
<storage-account-name>placeholder value with the name of your storage account. - Replace the
<source-path>placeholder with a path to the location of the files that you want to upload.
- Replace the
-
Find the public URL of your static website.
` az storage account show -n
-g --query "primaryEndpoints.web" --output tsv` Copy the URL in the output. The
https://<static_website_url>/public.keyis the public key URL.
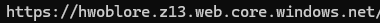
- Open browser and type in URL
https://<static_website_url>/public.key. The browser should display public key definition.
3. Create an OKTA developer account:
- Sign up for an OKTA developer account
4. Create a new app integration in OKTA:
- Sign in to the OKTA admin dashboard.
-
Note the URL https://{your OKTA domain}-admin.okta.com/.
-
Note the
{yourOktaDomain}. -
Create a new app integration with the following details.
| Application Property | Value |
|---|---|
| Sign-in method | OIDC - OpenID Connect |
| Application type | Single-Page Application |
| Grant type | Authorization Code, Interaction Code |
| Sign-in redirect URIs | http://localhost:5000/ |
| Sign-out redirect URIs | http://localhost:5000/signout |
| Trusted origins | http://localhost:5000/ |
| Assignments | allow access to specific users or groups based on your requirements |
-
After creating the app integration, note its Client ID
-
This sample app uses the OKTA sign-in widget which relies on the Interaction Code sign-in flow. To enable the Interaction Code flow:
-
Navigate to the API settings page under Security -> API
-
Under the Authorization Servers tab, note the default authorization server Name -
{yourOktaAuthServer}. -
Edit the default authorization server. Under Access Policies, edit the default policy rule
-
Under IF Grant type is -> Other grants, click on Interaction Code. Update the rule
-
Verify that CORS has been enabled for your base URL. On the same API page, under the Trusted Origins tab, base URL of the app i.e.
http://localhost:5000/should appear under Trusted Origins with CORS and - Redirect enabled. In case base URL is missing, add the URL i.e.http://localhost:5000/with CORS and Redirect enabled.
Setup manual authentication in Copilot Studio and D365 Omnichannel:
This section assumes that Copilot handoff to Dynamics 365 Customer Service is configured.
D365 Omnichannel:
-
Create a chat authentication setting record in the D365 Admin App.
-
In the site map of Copilot Service admin center, select Customer Settings.
-
In the Authentication settings section, select Manage.
-
Select New Authentication Settings, and then provide the following information on the Add authentication setting page:
Application Property Value Name Enter a name for the authentication setting. Owner Accept the default value or change it to a required value. Authentication type By default, OAuth 2.0 can’t be edited. Public key URL https://<static_website_url>/public.keyJavaScript client function auth.getAuthenticationToken -
In Copilot Service admin center, edit the chat widget in the Workstream settings, and then go to the Behaviors tab.
-
In the Authentication settings box, browse and select the chat authentication record.
Copilot Studio:
-
In the Copilot Studio Settings select Security. Set Authentication to Authenticate manually.
-
Provide the following information on the Authentication page and click Save:
Application Property Value Redirect URL https://token.botframework.com/.auth/web/redirectService provider Generic OAuth 2 All other values String - placeholder -
In the Copilot Studio Topics select System. Click on Sign In topic.
-
Click on More and select Open code editor.
Use pass-through pattern.
In this pattern, only the token and not the JWT payload (typically includes information about the authenticated user, such as their identity, attributes etc.) is sent to Copilot Studio. In addition, the token is not validated by Copilot till it is used e.g.to cal an API. Authentication flow works as long as Copilot Studio receives the token.
-
Copy YAML code from
/copilot/SingIn - Pass Through Pattern Flow.YAMLfile and paste in the code editor. Save topic. -
Publish the agent.
Use introspection API.
OPTIONAL - Steps [7], [8], [9] are to be followed only when implementing introspection API pattern.
In this pattern, the token is sent to Copilot Studio. The Copilot Studio calls the Idp instrspection API to validate the token and get the JWT payload (typically includes information about the authenticated user, such as their identity, attributes etc.). The authentication flow validates the token at the time of SSO.
-
Copy YAML code from
/copilot/SingIn - Introspection Flow.YAMLfile and paste in the code editor. -
Replace the following placeholder in the code. Save topic.
Placeholder Value Env.cat_OktaValidationURL https://{yourOktaDomain}/oauth2/Env.cat_OktaValidationURI) {yourOktaAuthServer}/v1/introspectEnv.cat_OktaClientId Client ID of Okta app noted above. -
Publish the agent.
5. Update constants in the sample app:
-
Update environment variable in
.envfile in the root folder. Save the file after updates.Placeholder Value AZURE_DEFAULT_DOMAIN http://localhost:5000OKTA_ORG_URL https://{yourOktaDomain}.okta.comOKTA_CLIENT_ID The Client ID of the OKTA application noted above. OKTA_SCOPES okta.users.readOKTA_REDIRECT_URI http://localhost:5000OKTA_AUTHORIZATION_SERVER default
Test the SSO flow:
Follow the demo steps below to test SSO flow -
Step 1: Note the Okta username of the test user.
![Go to `https://[Default domain]`](images/OktaUserName.png)
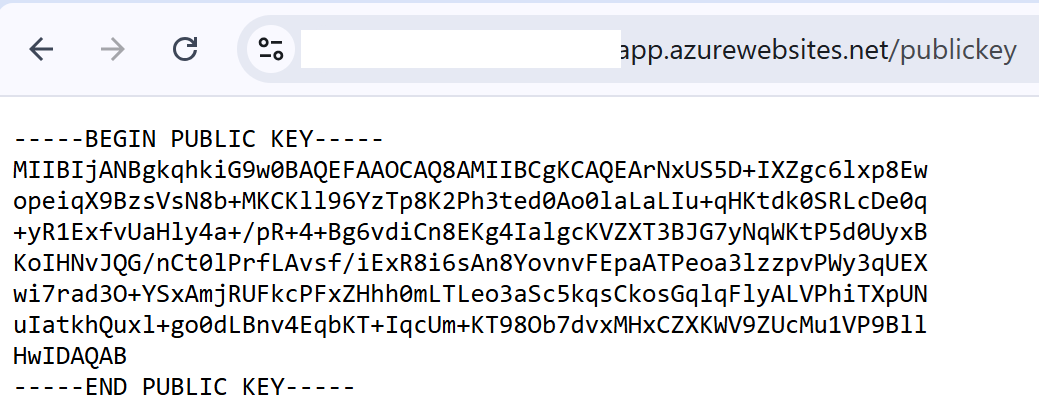
Step 2: Navigate to your project directory and run app.
`node app.js'
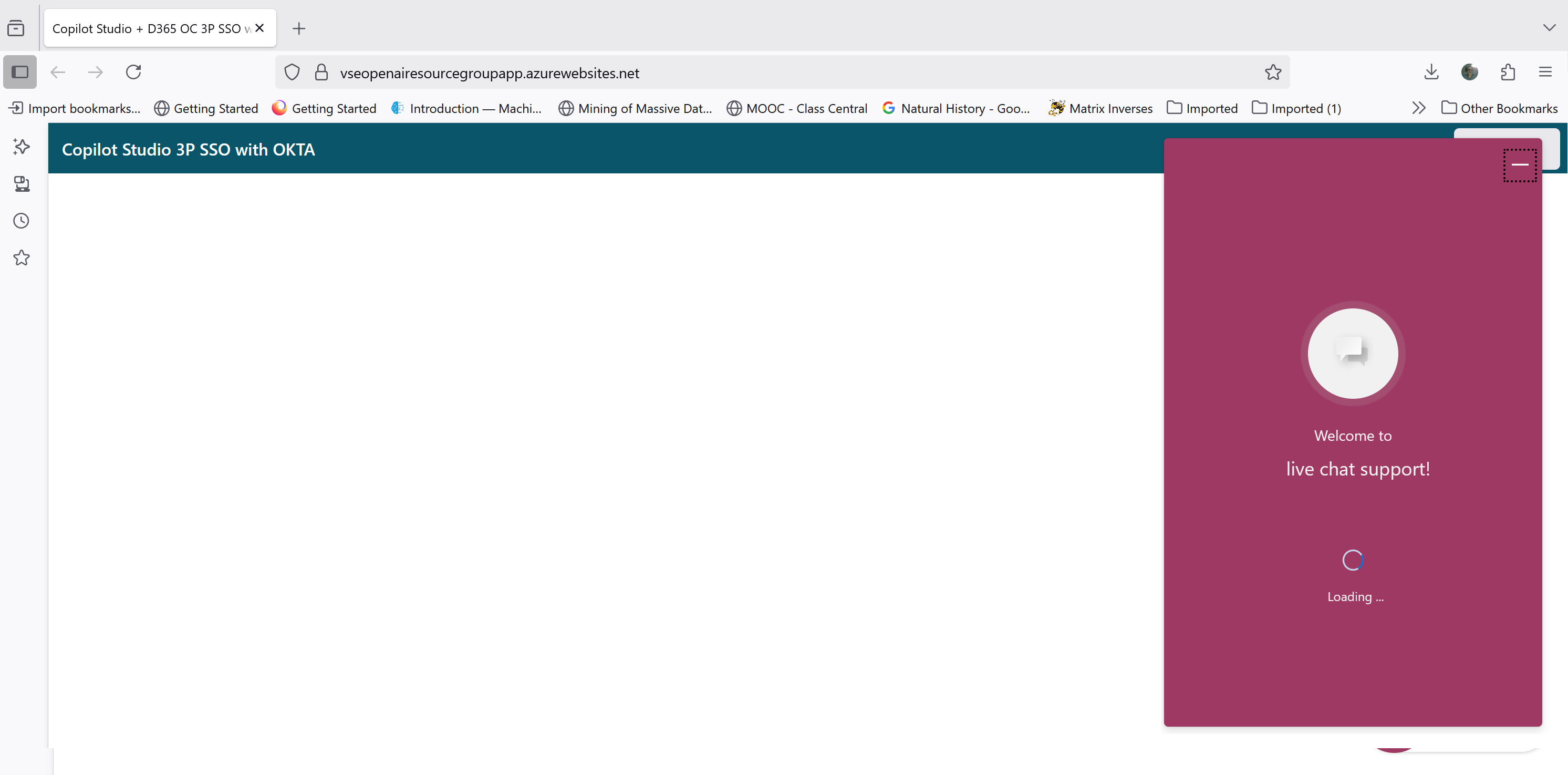
Step 3: Go to http://localhost:5000. Log in using Okta Credentials as test user. </em>
![Go to `https://[Default domain]`](images/Step1GotoToLogin.png)
Step 4: Verify login. Logout button would be visible.
Step 5: Once logged in; click on the chat widget top open.
Step 6: Agent displays Okta identification message with username of the test user. This step confirm Copilot Studio authentication.
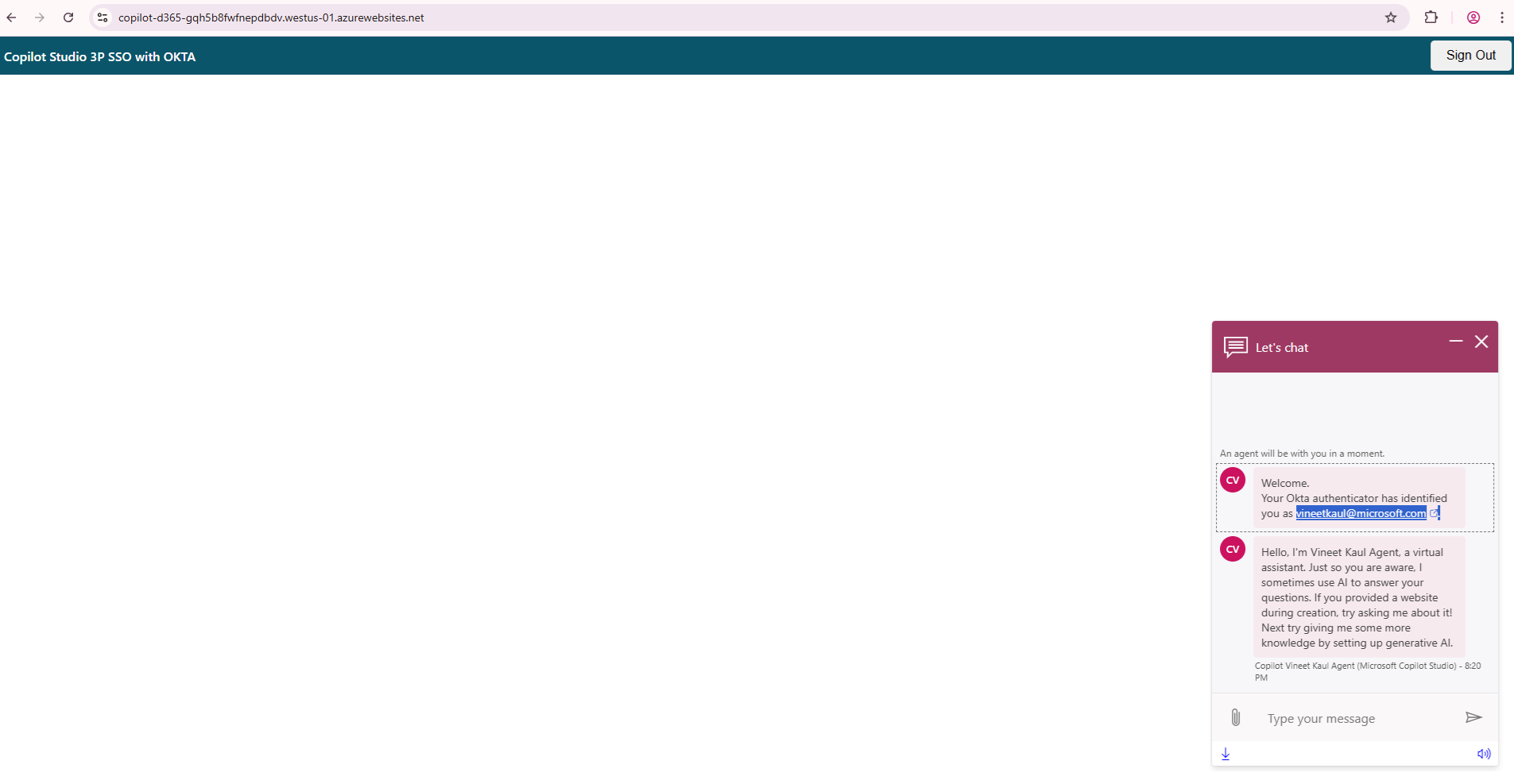
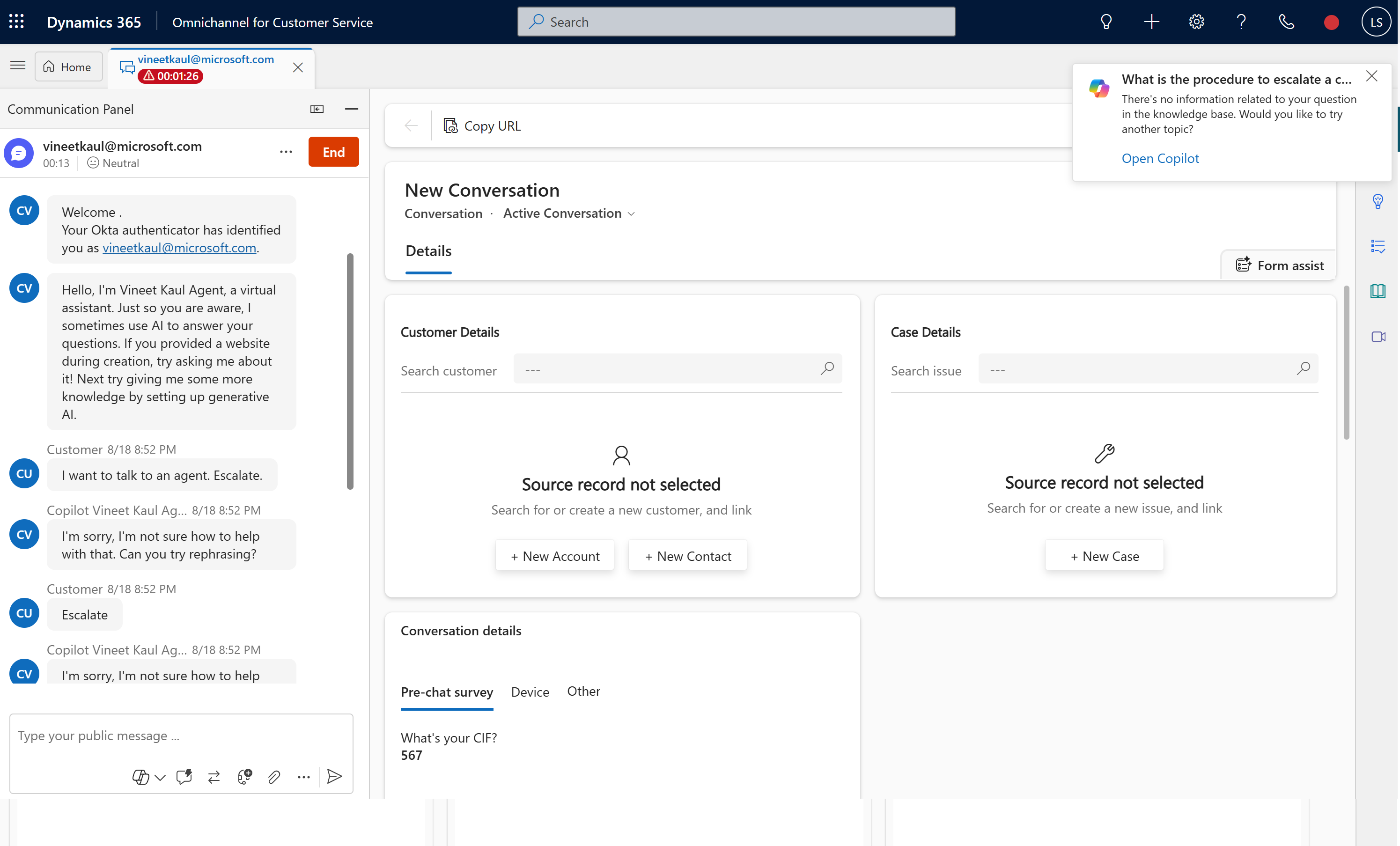
Step 7: Type i want to talk to an agent in chat window to transfer / handover chat to D365 Omnichannel.
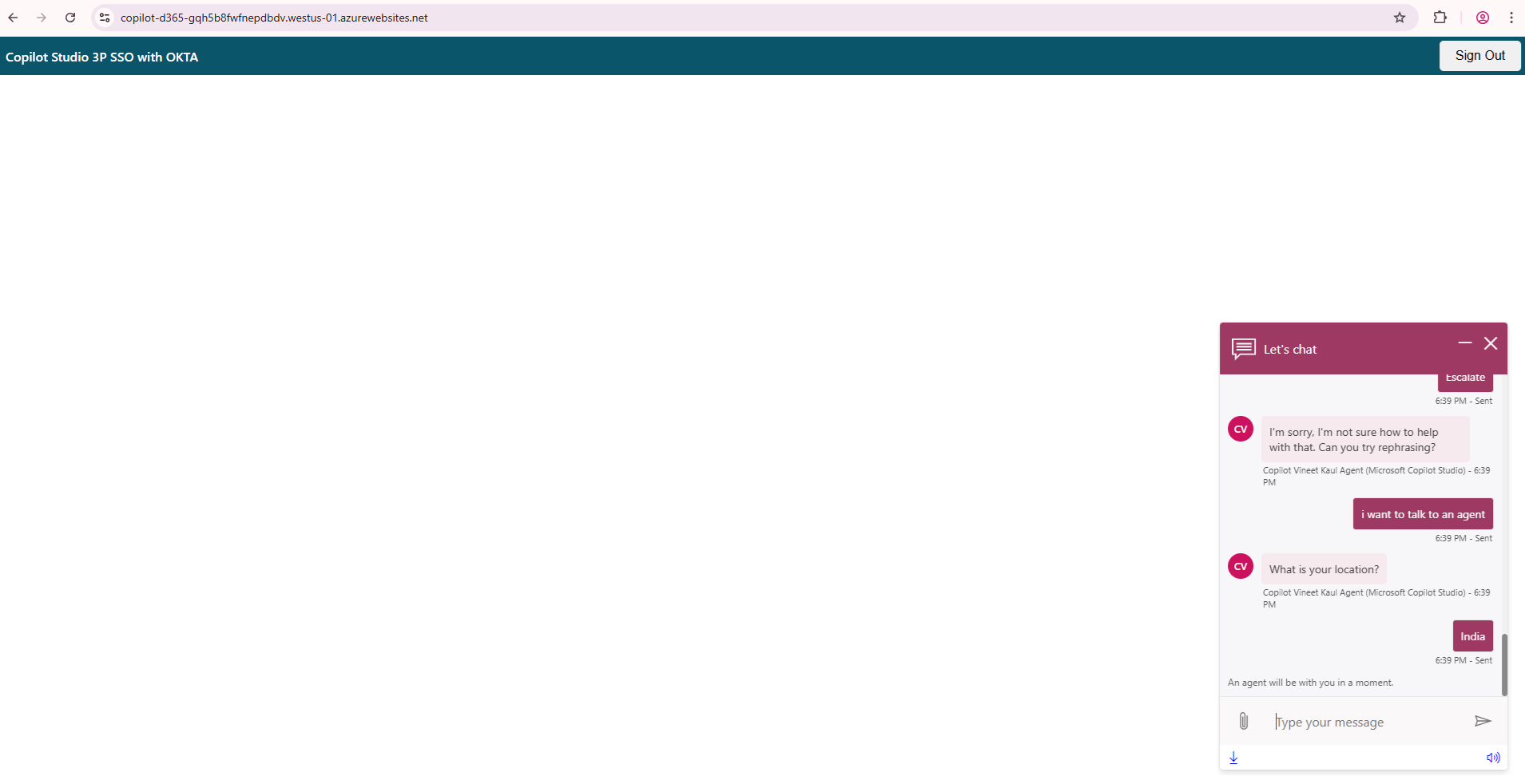
Step 8: Check Live Agent is available from Presence Status.
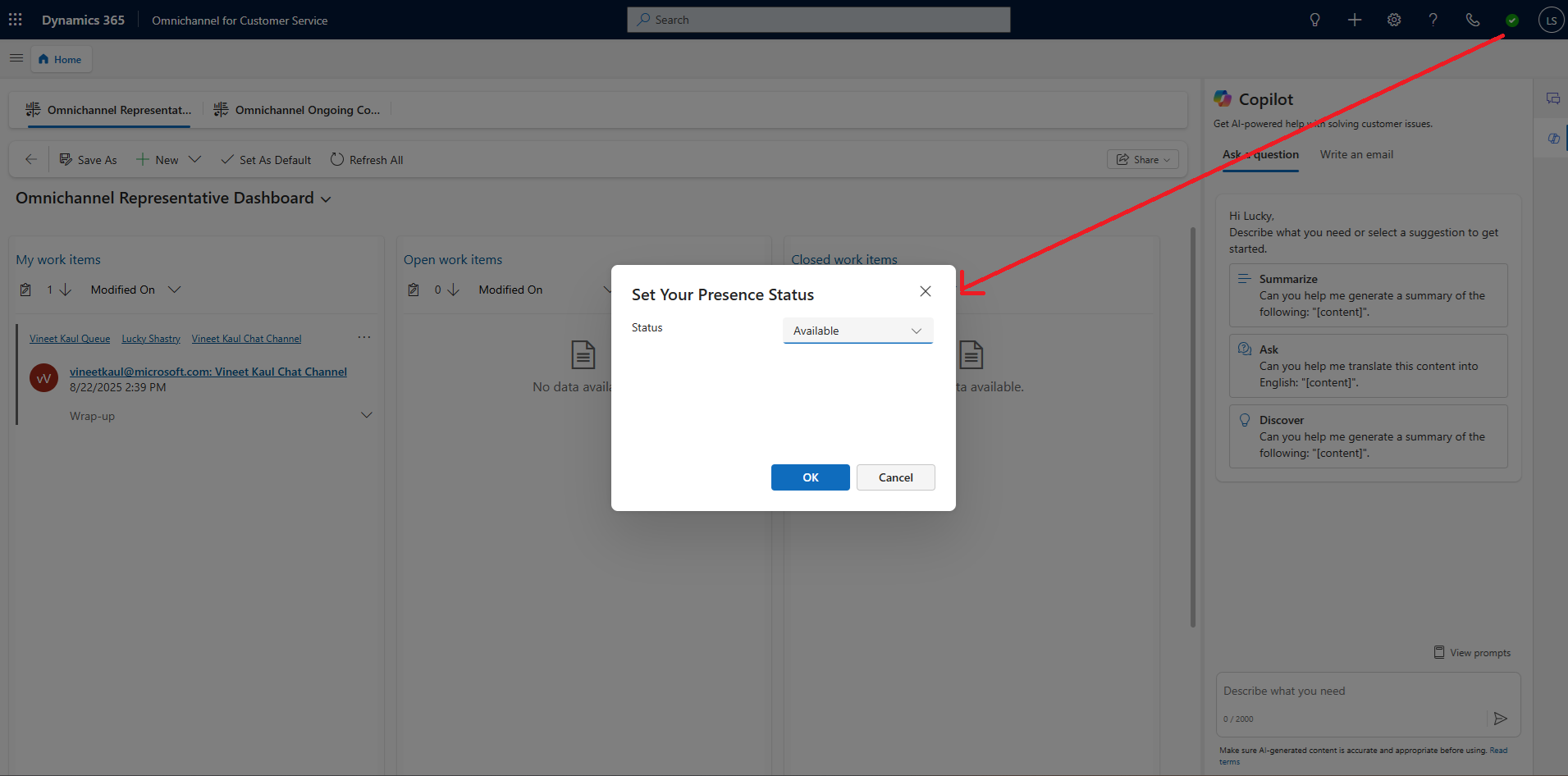
Step 9: Open Omnichannel for Customer Service console in D365 Service. A chat request notification pops with username of the test user. This step confirm D365 Omnichannel authentication.
Rewrite utterance
i want to talk to an agentin chat widget if chat request notification does not come up.
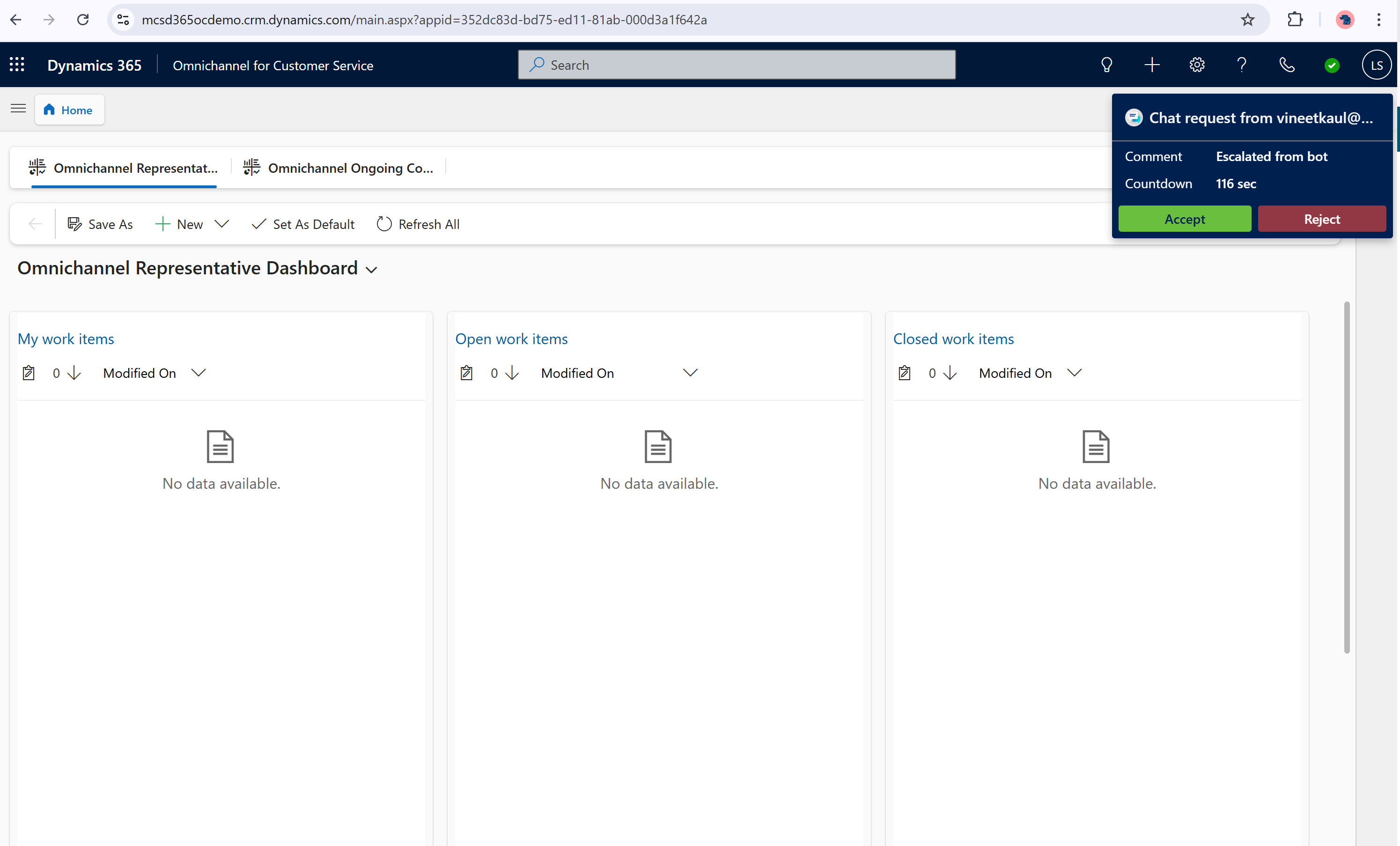
Step 10: Click on accept button. Chat window opens up with Okta username for Copilot & D365 Omnichannel.