

How to Use
The top row designates the tactic being used and the rows below it are the specific techniques pertaining to that tactic. Clicking on a specific tactic will list the techniques specific to it. Clicking on a specific technique will bring you to the page on that technique and the details around it.
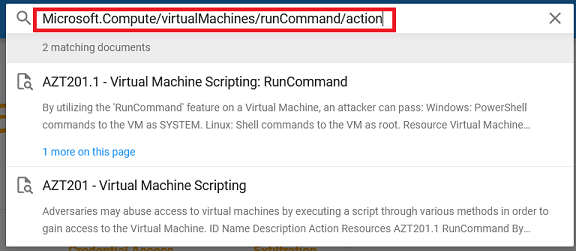
You can also utilize the search bar at the top to recursively search for specific text. For example, to search for what techniques a certain action or permission has, just enter the action in the search bar and it will show all relevant techniques.
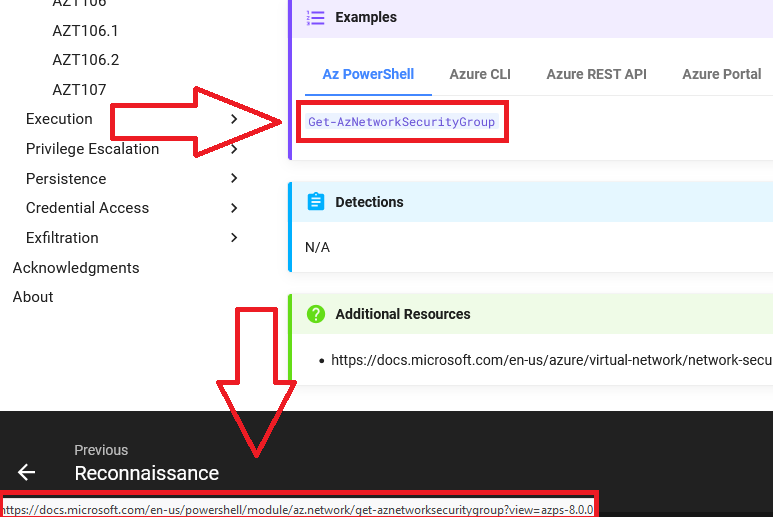
When viewing the page of a technique, specific examples of how to abuse the technique with different methods are shown. By clicking on the given command, it will bring you to the documentation around it.
Disclaimer
The purpose of the Azure Threat Research Matrix (ATRM) is to educate readers on the potential of Azure-based tactics, techniques, and procedures (TTPs). It is not to teach how to weaponize or specifically abuse them. For this reason, some specific commands will be obfuscated or parts will be omitted to prevent abuse.
New Technique Proposal
Have an idea for a new technique? Fill out the form here and we will contact you within 48 hours on further steps.
Feedback
With the intent of ATRM being a collaborative effort with the community, feedback is greatly appreciated. Is there a new or missing technique? Is the formatting off-putting? Please let me know @haus3c.