Microsoft DLP User Education & User Experience⚓︎
Purpose⚓︎
The purpose of this document is to educate end users on the end user experience across O365 DLP when a violation occurs.
Context⚓︎
Based on the service consumed by the user, a user might be blocked from doing certain action on the various channels covered by O365 DLP, the purpose of this document is to educate on how to react in case a violation occurred, and an action is required, by doing this user will be familiar with the procedure and will get educated.
Channels Covered by O365 DLP
- Device (Your corporate desktop)
- Exchange Online (Your mailbox)
- SharePoint / OneDrive (your corporate shared / personal storage)
- Teams (Your corporate collaboration platform)
Notifications on your desktop when using or reproducing sensitive content:
Based on your activities on the device, you (the end user), might violate a corporate policy for certain content of data being exfiltrated based on various activities on the endpoint, the list of activities that might trigger an action are the following:
- Upload to cloud service domains or access by unallowed browsers
- Copy to Clipboard
- Copy to a USB removable media.
- Copy to network share.
- Access by unallowed apps
- Transfer via Bluetooth
- Remote Desktop Services
Based on the corporate policy some actions from the above list may trigger an audit action, block restriction, or block with an option to override.
To get familiar with the look and feel the Block & Block with override activities the following Toast message (right low corner) will pop up when a violation occurs.
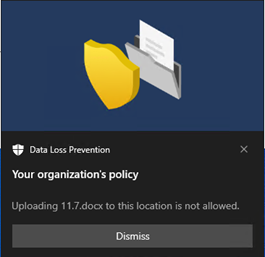
Block with no override option
When blocked without an option to override, a user violating a policy will get the following a popup message (toast message):
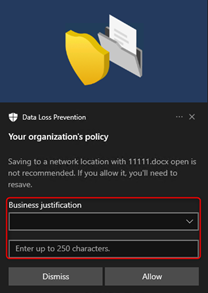
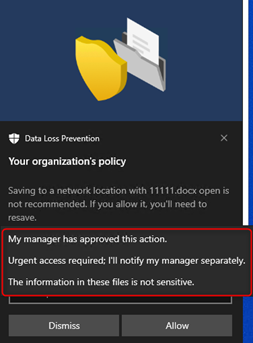
Block with override option
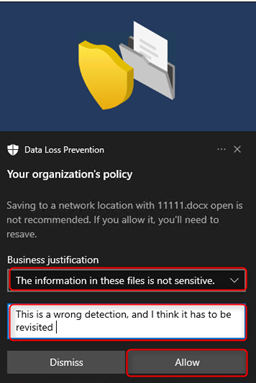
When blocked with an option to override, an administrator might allow you to pick from a pre-defined list of options with an option to input a customized text:
Notifications on your outlook when sharing sensitive content⚓︎
When sending an email with sensitive data, this email might be rejected from being sent out to the recipient. Based on the policy setting, you may get a message prior the sent out with a Policy Tip notifying that your about to violate a DLP policy and it might be blocked.
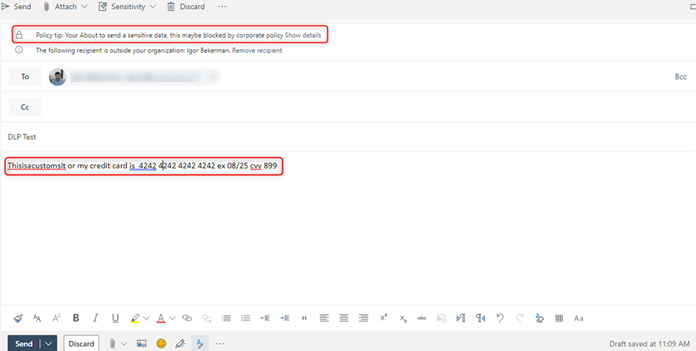
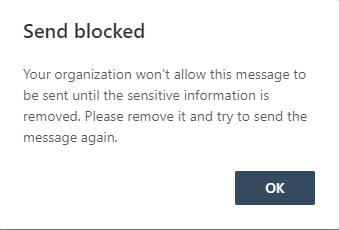
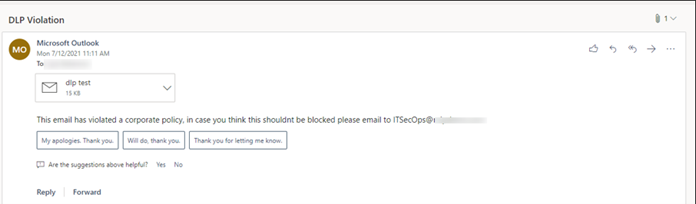
In some use cases you might be able to send the message and you will get blocked on post send, by configuration a user might get a notification that details the violating message and action taken with an explanation (configured by the corporate administrator).
Notification on Microsoft Teams when sharing sensitive content⚓︎
A DLP policy helps organizations prevent data loss. It also helps users to make better decisions when sending Sensitive Information Types knowingly or unknowingly. Currently, Teams-DLP supports protecting data while sharing a message or a file that contains sensitive information via 1-1 Chat or through channel messages.
Protecting Sensitive Information in Messages:
If someone is trying to share a chat message that contains sensitive information to an external user/guest, based on the creation of DLP-Rule for the Teams workload, the message will be blocked within seconds. Both the sender and receiver see the message blocked notification.
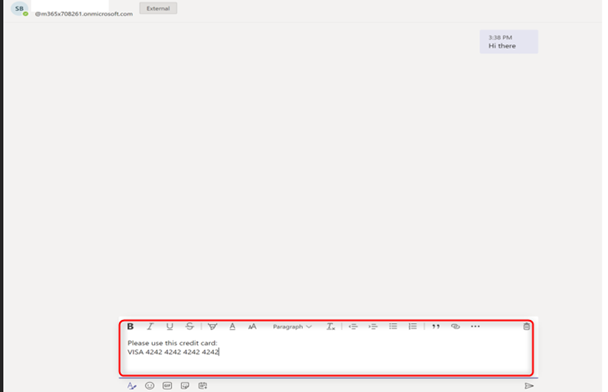
User Experience Sender’s Screen:
The Sender is attempting to send credit card information to the newly created federation user via 1-1 chat:
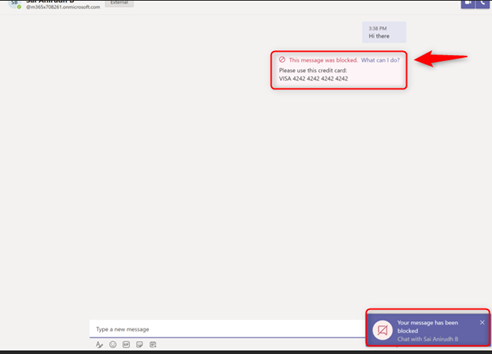
The message is blocked as the DLP rule is activated and the sender is notified:
Receiver Screen:
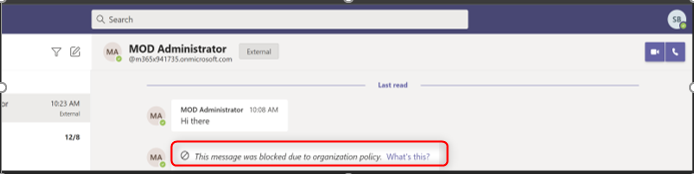
The receiver gets a blank blocked message, as shown below. Please note that there will be a delay of a few seconds in blocking the message and which is normal behavior (passive DLP).
Teams DLP end user experience - Video
Protecting Sensitive Information in Documents Sharing:⚓︎
If a user attempts to share a document that contains sensitive information with external users/guests in a Microsoft Teams Channel or chat, the DLP rule prevents opening the document by the external user. Note that, in this case, the DLP policy must include SharePoint and OneDrive locations for protection to be in place.
SharePoint / OneDrive Online
In SharePoint and OneDrive Online as a user you might share files and documents with internal and external entities, based on your organizational settings you might violate corporate policy with an action of notifying or blocking your documents / files from being shared.
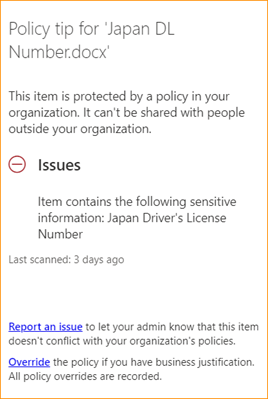
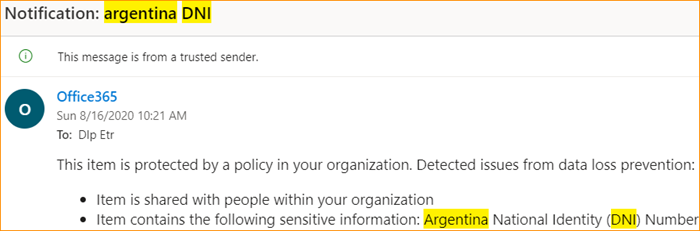
In case of a policy violation, you might receive an email + Policy Tip detailing the violation and the desired course of action.
For example, a red triangle will appear near to a file that violated a policy (Argentina National identity number)

An email explaining the violation might be sent to you as a user.
And a policy tip might appear as well.
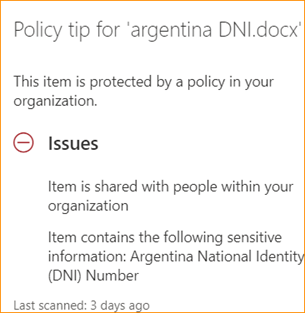
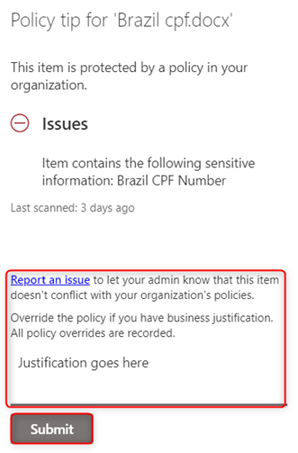
In some cases your admin might configure the ability to override a violating file / document, in such scenario before overriding the violating file will appear with the red triangle.

And after overriding the red triangle notification will be removed.

To override you need to select “Override the policy if you have a business justification, all policy overrides are recorded”.
In more severe cases your admin might set a policy that will block you from sharing a file containing sensitive content, in such case you will get a message stating that the file cant be shared and a “No entry” sign.

On sharing dialog:
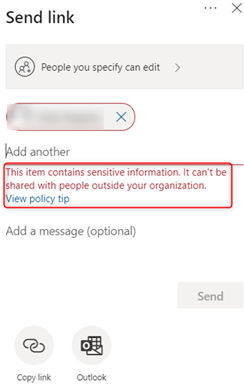
And a policy tip stating: