TIP
🔥 Help shape the future of Azure Tips and Tricks by telling what you'd like for us to write about here (opens new window).
💡 Learn more : Azure Defender overview (opens new window).
📺 Watch the video : How to use Azure Defender to protect hybrid cloud workloads (opens new window).
# How to use Azure Defender to protect hybrid cloud workloads
# A central place for security
Azure Security Center (opens new window) provides actionable security insights for all your Azure and non-Azure resources. It gives you an overall security score, and detects misconfiguration in resources, like open network ports, and more. Security Center is free to all Azure users. And in Azure Security Center, you can enable the Azure Defender feature (opens new window), which is a paid feature. Azure Defender provides advanced, intelligent protection of your Azure and hybrid resources. It lets you implement custom security policies and regulatory standards, like NIST (opens new window) and Azure CIS (opens new window), so that you can make sure that your resources comply to them, and what's needed to get them there. And it has a lot more advanced threat detection capabilities.
Azure Defender (opens new window) can defend resources in Azure, and also outside of Azure, like on-premises or in other clouds. In this post, we'll take a look at using Azure Defender to monitor my local, non-Azure machine.
# Prerequisites
If you want to follow along, you'll need the following:
- An Azure subscription (If you don't have an Azure subscription, create a free account (opens new window) before you begin)
- A local machine to install the Log Analytics Agent (opens new window) on
# Onboard non-Azure servers to Azure Defender
Let's get started by looking at Azure Security Center and onboarding my local machine. There are several ways to onboard a non-Azure resource to Azure Defender, including onboarding it to Azure Arc (opens new window), and using the AWS (opens new window) and GCP (opens new window) cloud connectors. We'll connect my local machine to a Log Analytics workspace (opens new window) that has Azure Defender enabled.
- Go to the Azure portal (opens new window)
- Open the Azure Security Center
- Navigate to the Inventory menu. This shows all the resources that Security Center is monitoring. From here, you'll get an overview of the health of your resources, and which ones aren't being monitored
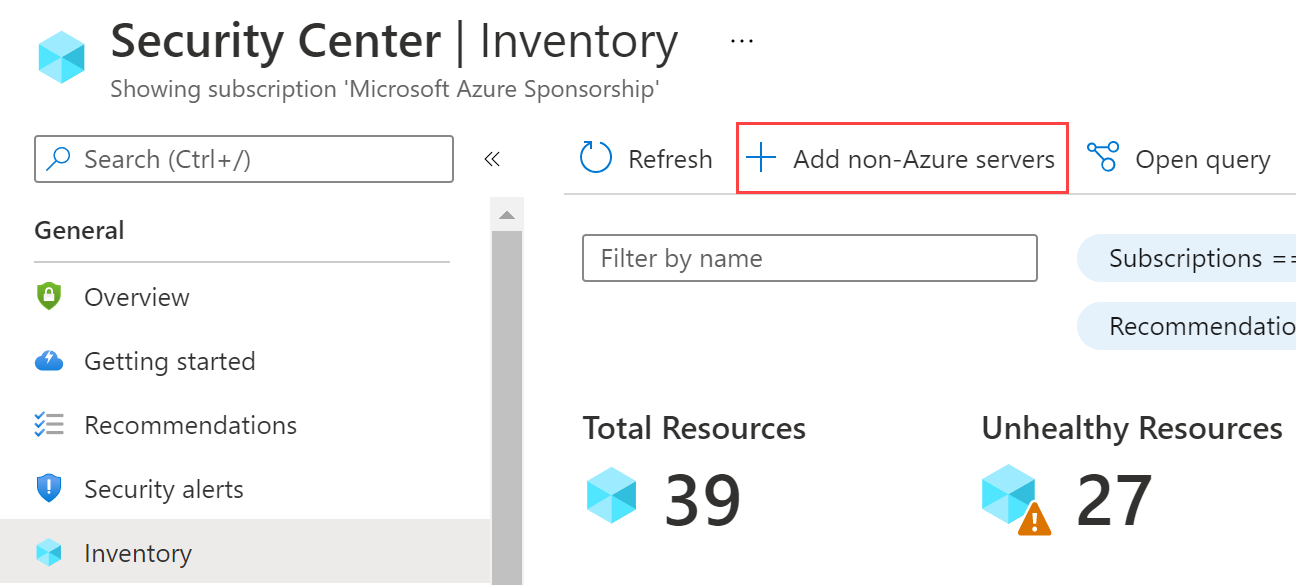
(Azure Security Center Inventory)
- Let's add my machine. Click on the Add non-Azure servers button. This takes you to the Onboard servers to Security Center blade. From here, you can connect servers to an Azure Log Analytics workspace, which connects with Security Center
- Click Create New Workspace
- Select a Resource group for the workspace
- Fill in a Name
- Pick a Region
- Select Review + Create and then Create
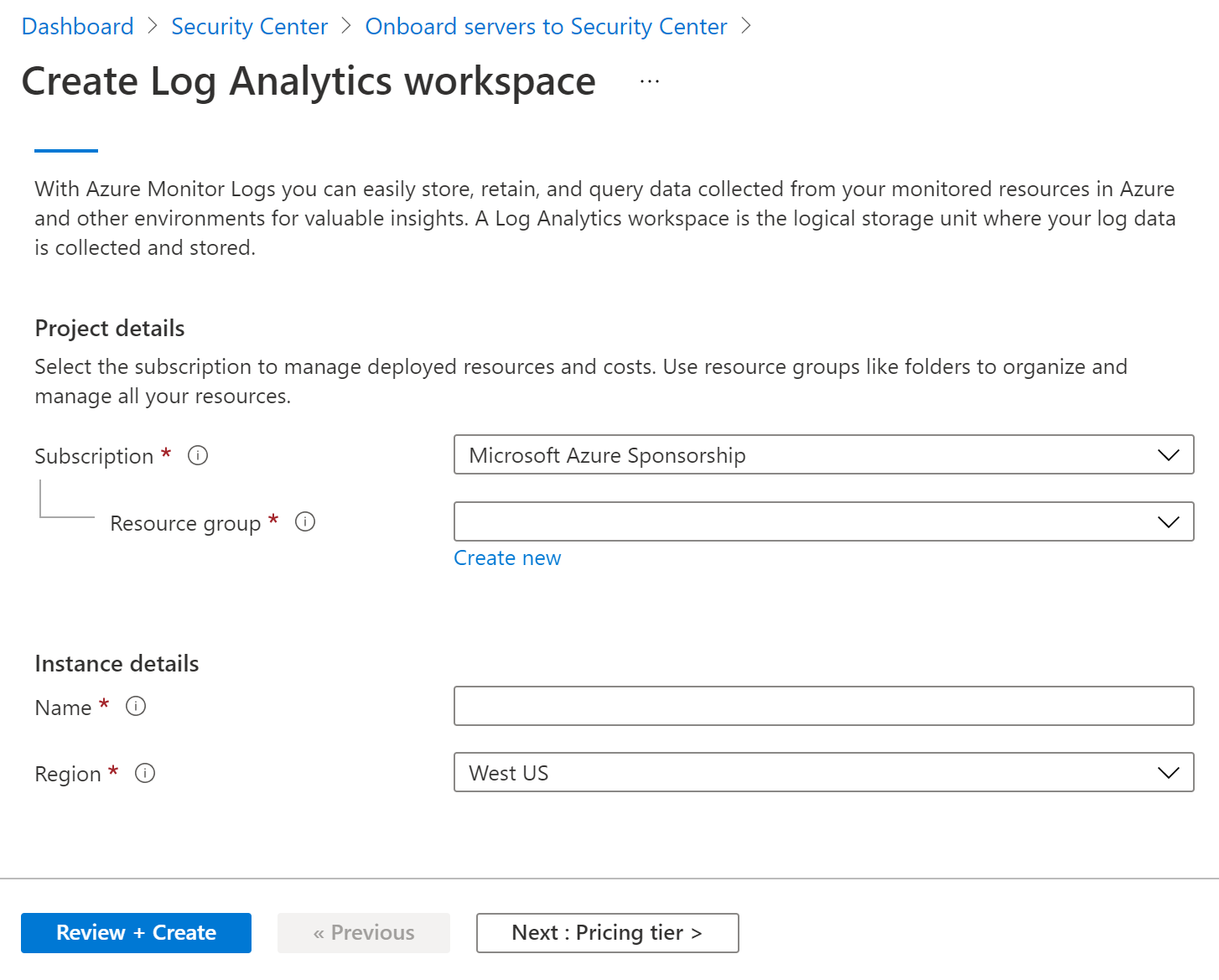
(Create a new Log Analytics workspace)
- When the Log Analytics workspace is created, it shows in the Onboard servers to Security Center blade. Click the Upgrade button to make sure that Azure Defender is activated for the workspace
- Next, click the Add Servers button of the workspace
- Now we can download a Log Analytics Agent for Windows or Linux and install it. I have a Windows machine, so I click Download Windows Agent (64 bit). Download the one that works for your Operating System
- Open the downloaded file and go through the wizard
- On the welcome screen, click Next
- Read the License Terms and click I Agree
- Optionally select a location for the installation and click Next
- Check the Connect the agent to Azure Log Analytics (OMS) box and click Next
- Now fill in the Workspace ID and Workspace Key that you'll find in the Agents management blade of the Azure portal, and click Next
- Click Next again
- Finally, click Install to install the agent
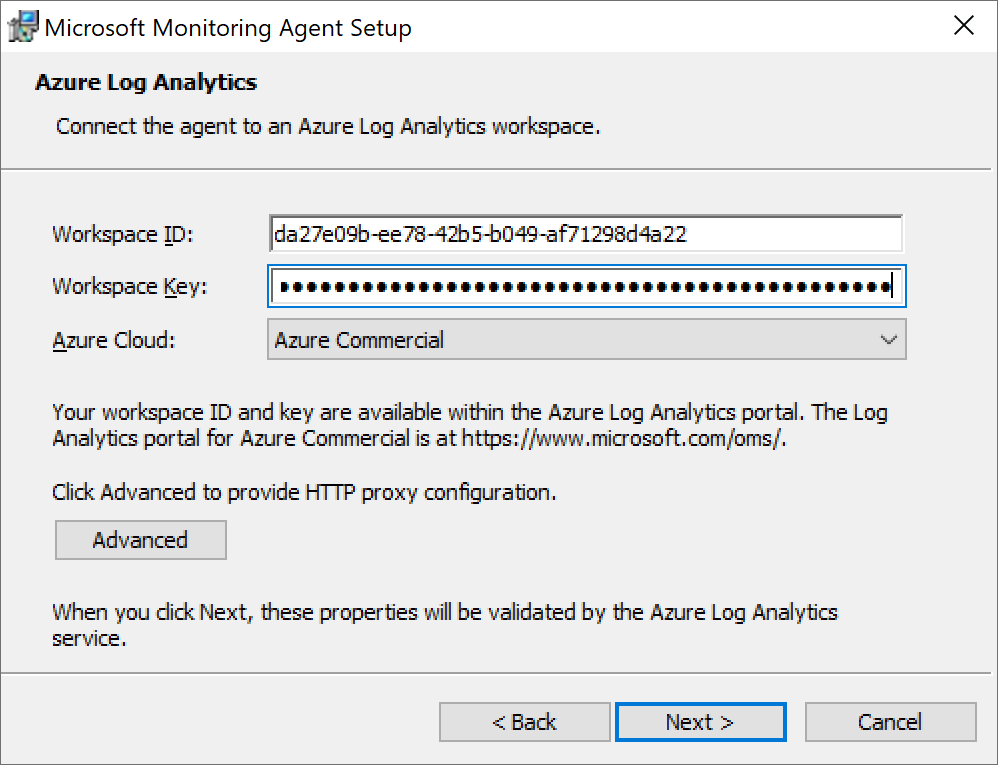
(Install the Azure Log Analytics Agent)
Your machine will show in the Azure Security Center when ready and be protected by Azure Defender. From there, you can drill down into and respond to any security recommendations.
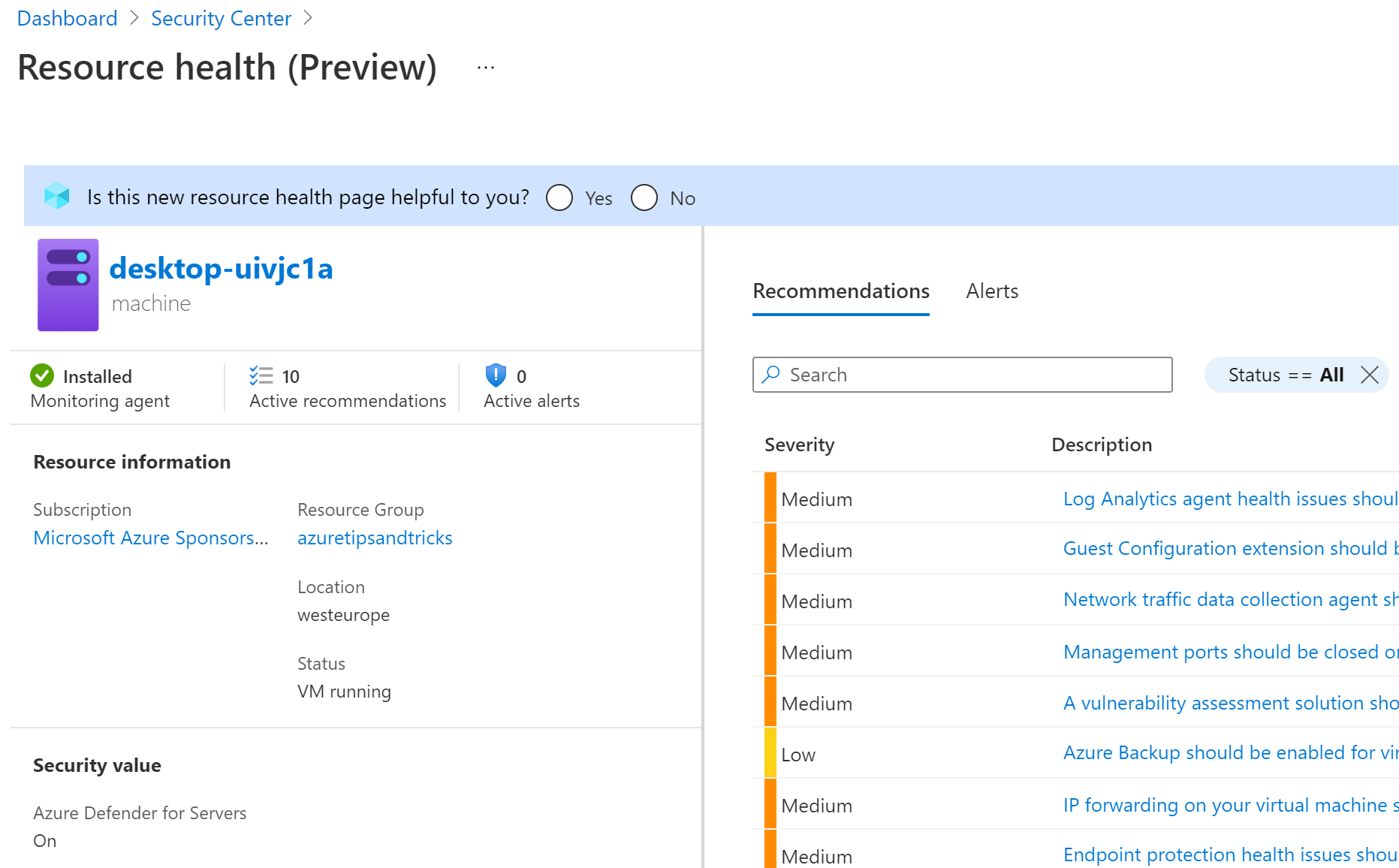
(My local machine protected by Azure Defender)
# Conclusion
Azure Defender (opens new window) is an advanced feature of Azure Security Center (opens new window). It provides intelligent security monitoring and detection capabilities for resources in Azure, on-premises and in other clouds. Go and check it out!
