Task 01: Create Azure Key Vault-backed secret scope for workspace
To reference the client secret stored in an Azure Key Vault, you can create a secret scope backed by Azure Key Vault in Azure Databricks.
-
Return to the browser tab that is signed into the Azure portal, go to the Home page.
-
Go to Resource groups > RG1 and select the Azure Databricks Service resource named, dbkws@lab.LabInstance.Id.
-
On the Azure Databricks Service page, in the Essentials section, copy the URL here:
@lab.TextBox(DBURL) -
Select Launch Workspace to authenticate your Azure credentials to the workspace.
Now that you have authenticated, you will create a secret scope for the workspace for secure access to the workspace.
-
Open a new browser tab and go to @lab.Variable(DBURL)#secrets/createScope.
This URL is case sensitive; scope in createScope must be uppercase.
-
Select Sign in with Microsoft Entra ID if prompted.
-
On the Create Secret Scope page, enter the following informatoin and then select Create.
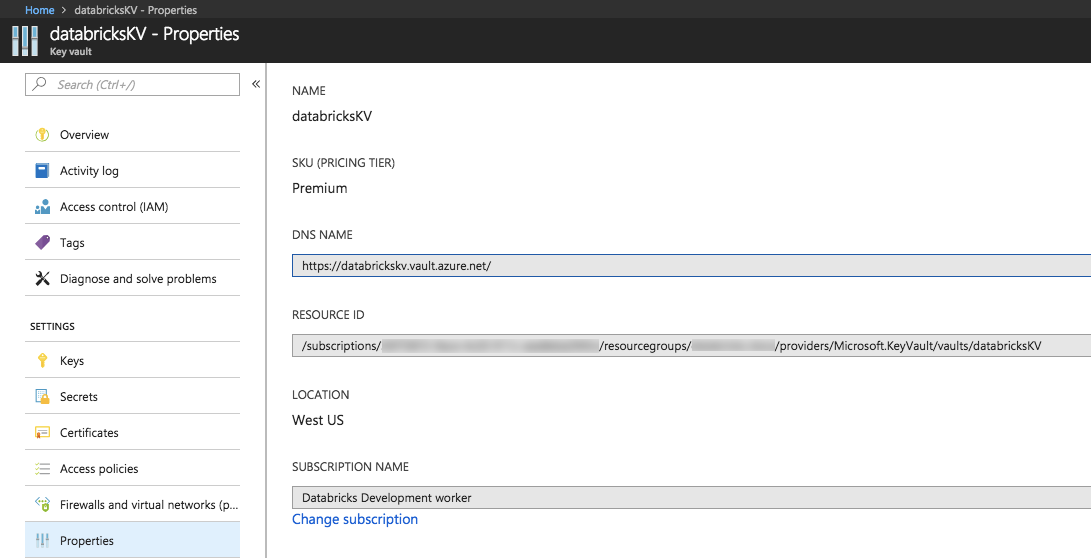
Default Value Scope Name scopesecret Managing Principal All workspace Users Azure Key Vault settings DNS Name [Your Azure Key Vault DNS Name, e.g., https://your-keyvault-name.vault.azure.net/] Resource ID [Your Azure Key Vault Resource ID] 
These properties are available from the Properties tab of an Azure Key Vault in your Azure portal.
-
Select OK.
