Microsoft Sentinel
Explore Microsoft Sentinel videos with demos delivered directly to partners, relevant certifications, and further resources.
Explore our new Microsoft Sentinel Skill-up Training Plan🎉
Stay connected with the Microsoft Sentinel Blog.🔗
 |
Microsoft Sentinel in just 30 minutes Short on time? Learn the fundamentals of Microsoft Sentinel, why it’s a necessity for your Security Operations (SecOps) and threat protection, its unique value, core capabilities, data ingestion methods, and more with a thorough demo and in just 30 minutes. |
 |
NEW: Transition to Unified SOC: Deep Dive and Interactive Q&A for SOC Analysts🆕 Discover how to smoothly transition from Microsoft Sentinel to the new unified SecOps platform! |
 |
NEW: Microsoft Sentinel Repositories: Manage Your SIEM Content Like a Pro🆕 Explore how Microsoft Sentinel Repositories streamline content management, enable team collaboration, and now support Bicep templates for easier infrastructure-as-code. |
 |
Microsoft Sentinel Sizing, Pricing, and Planning Learn about what influences Microsoft Sentinel's costs, different pricing models, archive and long-term retention options, logs, and a demo of how to estimate and measure spend. |
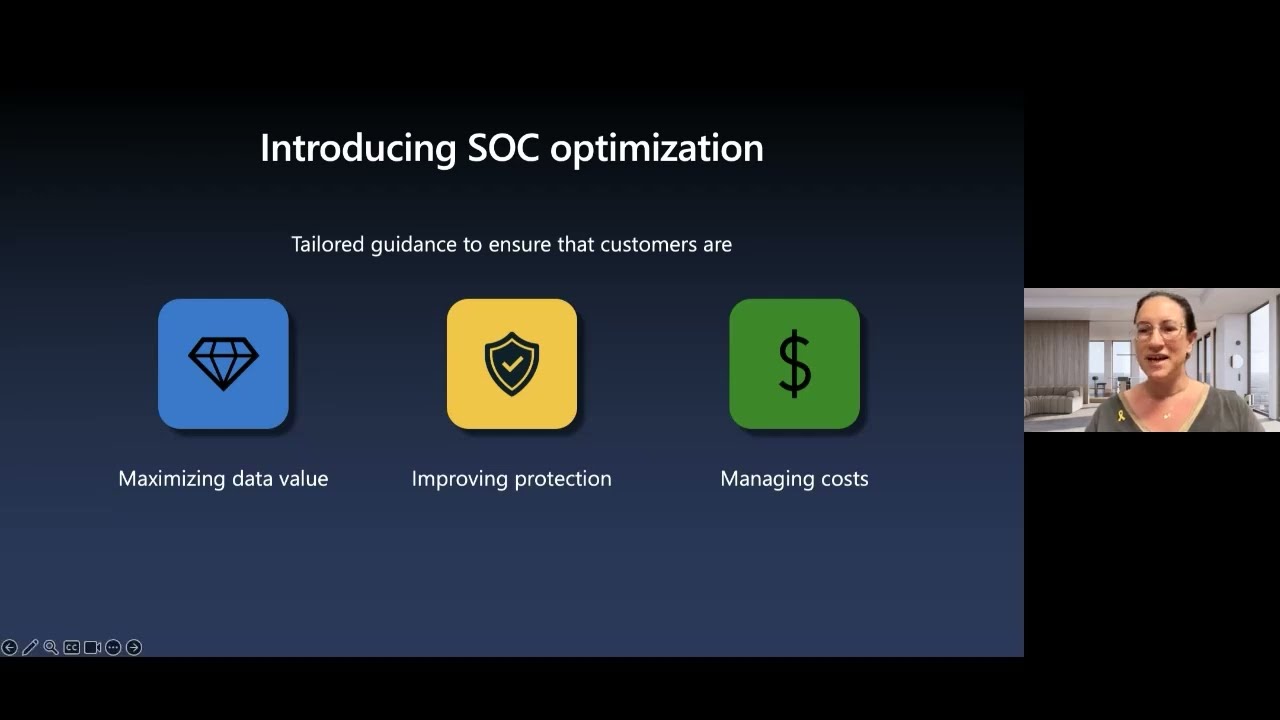 |
Optimizing SecOps: Manage Your Data, Costs, and Protections with SOC Optimizations Learn how data ingestion analysis offers tailored recommendations to optimize costs, maximize data value, and strengthen defenses against emerging threats, with real-world use cases and a live demo! |
 |
Splunk to Microsoft Sentinel Migration Experience Learn about the new Microsoft Sentinel feature that helps Splunk migrations, including migrating Splunk detections to Sentinel Analytic Rules. |
 |
Building Microsoft Sentinel Integrations Part 1: Onboarding Learn about creating Microsoft Sentinel integrations with other security products, including scenarios to consider and the steps and components involved. |
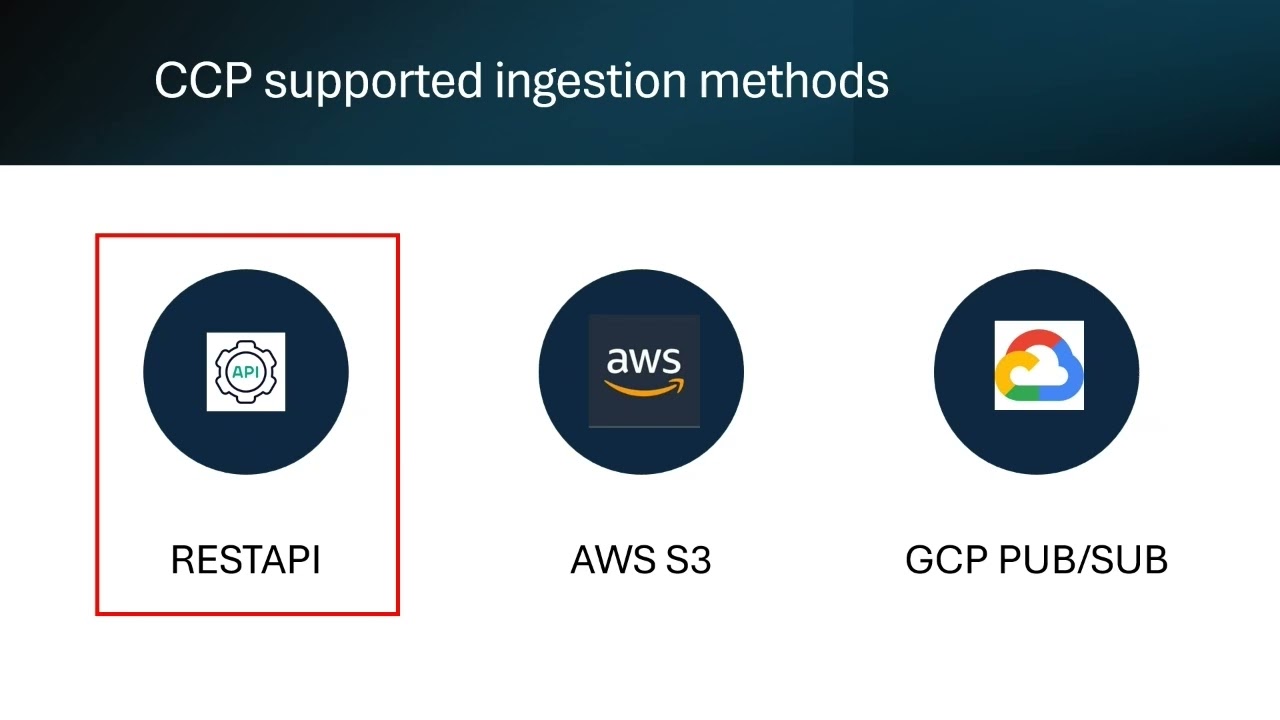 |
Building Microsoft Sentinel Integrations Part 2: Creating Data Connectors Explore the different connectors available for bringing data into Microsoft Sentinel, with analysis of the codeless connector platform that simplifies data ingestion without writing code. |
 |
Microsoft Sentinel Deep Dive SEPT. 2023 Update Bad actors and nation-states threaten critical infrastructure and industries with increasingly complex attacks. If you’re a Microsoft partner or MSSP, learn how to fight back with our comprehensive deep dive into Microsoft Sentinel. |
 |
Configuring Your Microsoft Sentinel Environment Learn how to configure your Microsoft Sentinel environment, including storage options, log management, and best practices for optimizing your SIEM setup. |
 |
All About Microsoft Sentinel UEBA Attackers often disguise their actions as normal activities, creating a grey area that may pose risks to your organization. Learn how UEBA builds comprehensive profiles of the user and entity across time and peer group horizons to find anomalies and suspicious activity. |
 |
All About Jupyter Notebooks and Hunting in Microsoft Sentinel Learn how to defend a multicloud, multi-SaaS environment with External Attack Surface Management (EASM), Microsoft Defender Threat Intelligence (MDTI), and threat hunting with Jupyter Notebooks. |
 |
All About Microsoft Sentinel Threat Intelligence and Investigation Explore various TI features within Microsoft Sentinel and learn about Sentinel’s advanced multistage attack detection with Fusion. Additionally, analyze basic incident investigations, including investigations across workspaces for MSSPs scenarios. |
 |
Automating Responses in Microsoft Sentinel Learn about Microsoft Sentinel’s SOAR capabilities, including Automation Rules and Playbooks. Explore several OOB Playbooks, Community Playbooks, as well as Custom Playbooks, including one utilizing the OpenAI Logic App Connector. |